
A few months ago, a boutique RIA principal we spoke with pulled up their firm's cybersecurity incident response plan on a shared drive. It was dated 2019, written for the way the company operated back then, and had never really been tested.
This firm is not the only one in this position. Most smaller advisory firms are also working with outdated frameworks. They also have the same deadline: June 3, 2026, to have a functional, documented cybersecurity program in place.
This post covers what the SEC's amended Regulation S-P requires, where most smaller firms are falling short, and why the deadline matters beyond the firms it directly regulates — including the family offices and UHNW clients whose financial lives are in those advisory systems.
What Is Reg S-P, and What Changed?
Regulation S-P has been part of the SEC's framework since 2000. It governs how financial institutions handle customer information: how they protect it, what they do when something goes wrong, and what they owe customers when their data is compromised.
The SEC amended the rule significantly in 2024. Larger covered entities had until December 2025 to comply. Smaller entities (i.e., those with under $1.5 billion AUM, smaller broker-dealers, transfer agents, and funding portals) have until June 3, 2026.
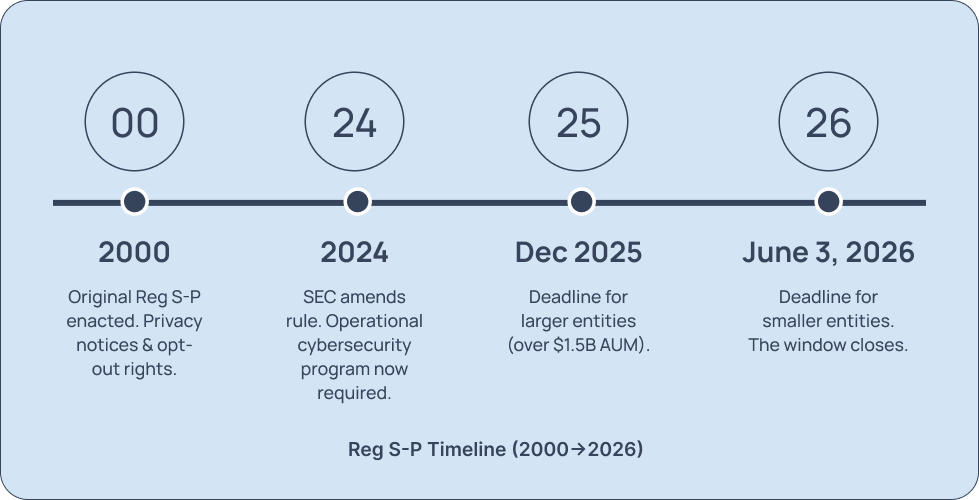
The amendment reflects a fundamental shift in regulatory expectation. Before the update, Reg S-P focused primarily on privacy notices and opt-out rights. The amended version adds a mandatory operational requirement: a documented, functioning cybersecurity incident response program that works.
Who Is Covered
broker-dealers
funding portals
investment companies
SEC-registered investment advisers
transfer agents
There are no exemptions for small firms, low transaction volume, or firms that outsource their IT. If your firm holds an SEC registration and falls below the $1.5 billion AUM threshold, the June 3 deadline applies to you.
What the Rule Requires
The amended Reg S-P imposes four concrete obligations that the SEC will examine for operational evidence.

1. Written Cybersecurity Incident Response Program
The rule requires policies and procedures "reasonably designed to detect, respond to, and recover from unauthorized access to or use of customer information" (17 CFR § 248.30(a)(3)). The SEC's standard is "reasonably designed,” that is, a functional, tested, operational program. A plan that's never been tested, reviewed, or updated doesn't meet this bar. The SEC expects something your staff can execute when something goes wrong.

2. 30-Day Customer Notification

3. Service Provider Notification Policies

4. Recordkeeping
Where Most Firms Are Falling Short
The gap between where most smaller firms are and where they need to be is usually structural.
Cybersecurity incident response programs that exist on paper only
A firm drafted a plan several years ago. It describes what the firm would do in a breach. But it hasn't been tested, updated after a staff change, or mapped to current systems.
Service provider oversight that's informal rather than documented
Many smaller firms have functional outsourced IT relationships. What they don't have is written oversight policies that document how those vendors are selected, monitored, and held to the firm's security requirements. The SEC will ask for documentation.
Recordkeeping that doesn't meet examination standards
Most firms have some logs. What they often lack is a structured, immutable recordkeeping system that meets the specificity the rule requires — incident documentation tied to dates, decisions, and outcomes, stored for the required retention period.
Access controls without a current asset inventory
You can't credibly claim to be monitoring for unauthorized access to customer data if you don't have a current map of where that data lives. Many firms are running access controls against an outdated picture of their own systems.
Why This Matters to Family Offices
Whether Reg S-P applies to your family office directly depends on how it's structured.
Direct Exposure
Single-family offices are generally excluded from SEC registration under Rule 202(a)(11)(G)-1, which defines family offices for purposes of exclusion from the definition of an investment adviser under the Advisers Act. But that exclusion has limits. Multi-family offices were required to register with the SEC as investment advisers following the Dodd-Frank Act, which means Reg S-P applies to them directly. Similarly, family offices that have expanded to manage or co-invest with outside capital may no longer qualify for the exclusion and may be required to register. Family offices that have voluntarily registered with the SEC are covered entities under the rule regardless of structure.
Indirect Exposure
For offices that fall outside the rule, indirect exposure is still real. The advisers and wealth managers you work with hold a detailed picture of your family's financial life: account structures, estate documents, transaction histories, beneficial ownership information. A breach in their systems can surface your family's data without your involvement in how it's handled — the investigation, the notification timeline, and any public enforcement record all sit with the regulated entity, not with you.
Either way, it's worth asking your advisers directly before June 3:
1
2
Who manages their service provider oversight policies?
3
How do they document breach investigations?
The quality of those answers matters.
The Enforcement Landscape
Under current SEC leadership, enforcement priorities have shifted away from minor recordkeeping violations and off-channel communications. Cybersecurity failures that lead to actual investor harm — stolen funds, identity theft, compromised accounts — remain a top priority.
Recent enforcement actions confirm the exposure.

In November 2025, a dually registered broker-dealer and RIA agreed to pay $325,000 to settle SEC charges tied to cybersecurity failures, including email account takeovers across more than 120 branch offices and missing multi-factor authentication. That's before remediation costs, legal fees, and the reputational damage that follows a public enforcement action.
Enforcement actions tend to target firms with no program at all, not firms that tried and fell short.
How Decypher Can Help
Decypher works with financial services firms across the full compliance process — from an initial gap analysis to a fully managed security operation. Depending on where your firm is and how much time you have, that can mean:
a focused readiness assessment before June 3
a complete cybersecurity incident response program build-out
ongoing managed detection
vendor oversight
compliance documentation that covers the monitoring obligations the rule doesn't let you satisfy once and forget
For context on investment: the cost of building a compliant program is a fraction of a basis point on the assets under management for most firms in this window. A breach, an enforcement action, or a failed examination costs considerably more — in remediation, legal fees, and the reputational damage that follows.

The deadline is June 3. There's still time.
